Microsoft has warned that adversaries are utilizing OAuth purposes as an automation device to deploy digital machines (VMs) for cryptocurrency mining and launch phishing assaults.
“Menace actors compromise person accounts to create, modify, and grant excessive privileges to OAuth purposes that they will misuse to cover malicious exercise,” the Microsoft Menace Intelligence workforce said in an evaluation.
“The misuse of OAuth additionally permits risk actors to take care of entry to purposes even when they lose entry to the initially compromised account.”
Beat AI-Powered Threats with Zero Trust – Webinar for Security Professionals
Conventional safety measures will not lower it in immediately’s world. It is time for Zero Belief Safety. Safe your information like by no means earlier than.
OAuth, brief for Open Authorization, is an authorization and delegation framework (versus authentication) that gives purposes the power to securely entry info from different web sites with out handing over passwords.
Within the assaults detailed by Microsoft, risk actors have been noticed launching phishing or password-spraying assaults in opposition to poorly secured accounts with permissions to create or modify OAuth purposes.
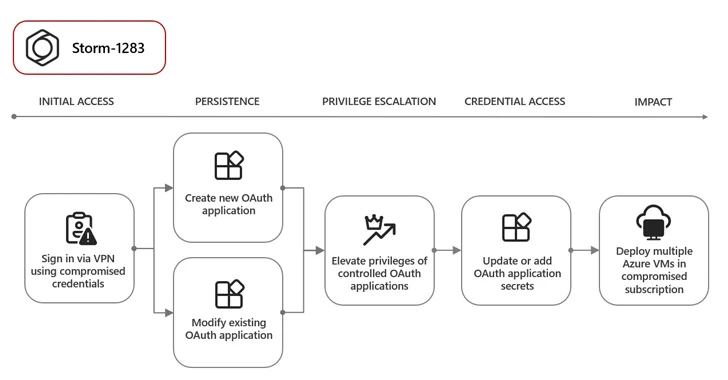
One such adversary is Storm-1283, which has leveraged a compromised person account to create an OAuth utility and deploy VMs for cryptomining. Moreover, the attackers modified current OAuth purposes to the account had entry to by including an additional set of credentials to facilitate the identical targets.
In one other occasion, an unidentified actor compromised person accounts and created OAuth purposes to take care of persistence and to launch e-mail phishing assaults that make use of an adversary-in-the-middle (AiTM) phishing package to plunder session cookies from their targets and bypass authentication measures.
“In some circumstances, following the stolen session cookie replay exercise, the actor leveraged the compromised person account to carry out BEC financial fraud reconnaissance by opening e-mail attachments in Microsoft Outlook Internet Utility (OWA) that comprise particular key phrases corresponding to ‘cost’ and ‘bill,” Microsoft mentioned.
Different situations detected by the tech large following the theft of session cookies contain the creation of OAuth purposes to distribute phishing emails and conduct large-scale spamming exercise. Microsoft is monitoring the latter as Storm-1286.
To mitigate the dangers related to such assaults, it is really helpful that organizations implement multi-factor authentication (MFA), allow conditional entry insurance policies, and routinely audit apps and consented permissions.