Key takeaways
- On April 1, 2026, attackers drained roughly USD 285 million in person belongings from Drift Protocol — the most important decentralized perpetual futures trade on Solana — in roughly 12 minutes, with most stolen funds bridged to Ethereum inside hours.
- On-chain staging started on March 11, practically three weeks earlier than the April 1 execution — with attacker infrastructure, token manufacturing, and social engineering all working in parallel with cautious coordination.
- The crucial vulnerability was not a wise contract bug however a mix of social engineering multisig signers into pre-signing hidden authorizations and a zero-timelock Safety Council migration that eradicated the protocol’s final line of protection.
- The attacker manufactured a completely fictitious asset — CarbonVote Token — with a couple of thousand {dollars} in seeded liquidity and wash buying and selling, and Drift’s oracles handled it as legit collateral value a whole bunch of thousands and thousands of {dollars}.
On April 2, 2026, Drift Protocol confirmed that attackers drained roughly USD 285 million in person belongings on April 1, 2026. That is the most important DeFi hack of 2026 — and the second-largest exploit in Solana’s historical past, behind solely the USD 326 million Wormhole bridge hack in 2022. TRM’s preliminary investigation suggests the hack was possible perpetrated by North Korean hackers.
What’s Drift, and the way precisely did this occur?
Drift is the most important decentralized perpetual futures trade on the Solana blockchain, permitting customers to commerce leveraged positions with out a centralized middleman. It held billions in person belongings, which made it a high-value, high-complexity goal.
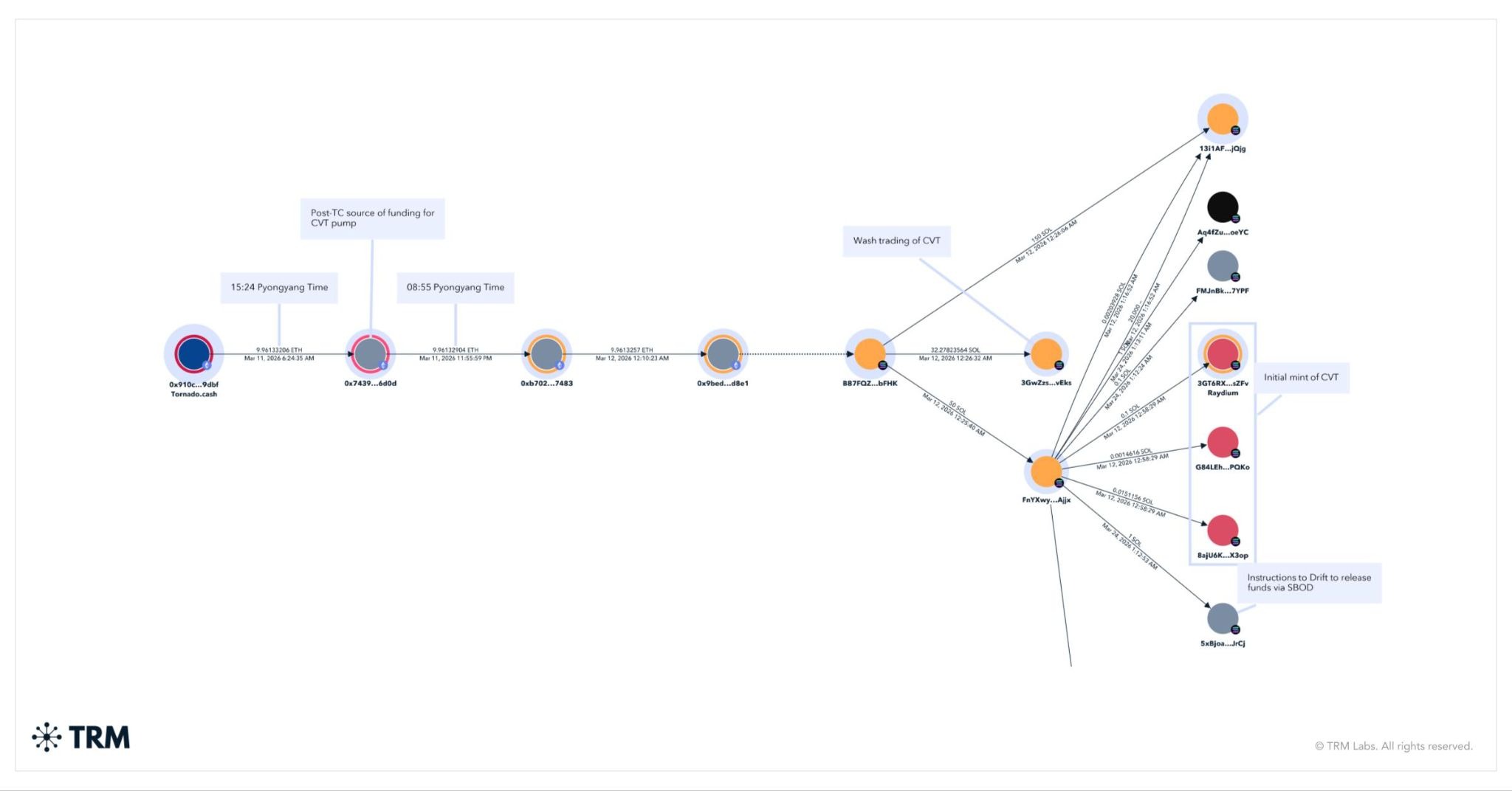
The assault didn’t start on April 1. On-chain staging started weeks earlier, on March eleventh, with a single withdrawal of 10 ETH from Twister Money. These ETH started shifting hours later at round 12:00 AM GMT on March twelfth – or round 09:00 Pyongyang time – and shortly after funded the deployment of CarbonVote (CVT), the token used to govern Drift.
Between March 23 and March 30, the attacker created a number of “sturdy nonce” accounts — a legit Solana function that enables transactions to be pre-signed and executed later with out expiring. The attacker used social engineering to induce Drift Safety Council multisig signers into pre-signing transactions that appeared routine however carried hidden authorizations for crucial admin actions.
On March 27, Drift migrated its Safety Council to a brand new 2/5 threshold configuration with zero timelock — eliminating the delay that might have allowed detection and intervention. That migration created the exploitable hole.
In parallel, the attacker spent weeks manufacturing legitimacy for a faux token — CarbonVote Token (CVT) — minting 750 million items, seeding only a few thousand {dollars} in liquidity on Raydium, and utilizing wash buying and selling to construct a value historical past close to USD 1. Drift’s oracles picked up that synthetic sign and handled CVT as an actual asset.
On April 1, these pre-signed transactions had been deployed. The attacker listed CVT as legitimate collateral on Drift, raised withdrawal limits to excessive ranges, and deposited a whole bunch of thousands and thousands in CVT in opposition to that manufactured value. Then 31 withdrawal transactions executed in roughly 12 minutes — draining actual belongings together with USDC and JLP from the protocol.
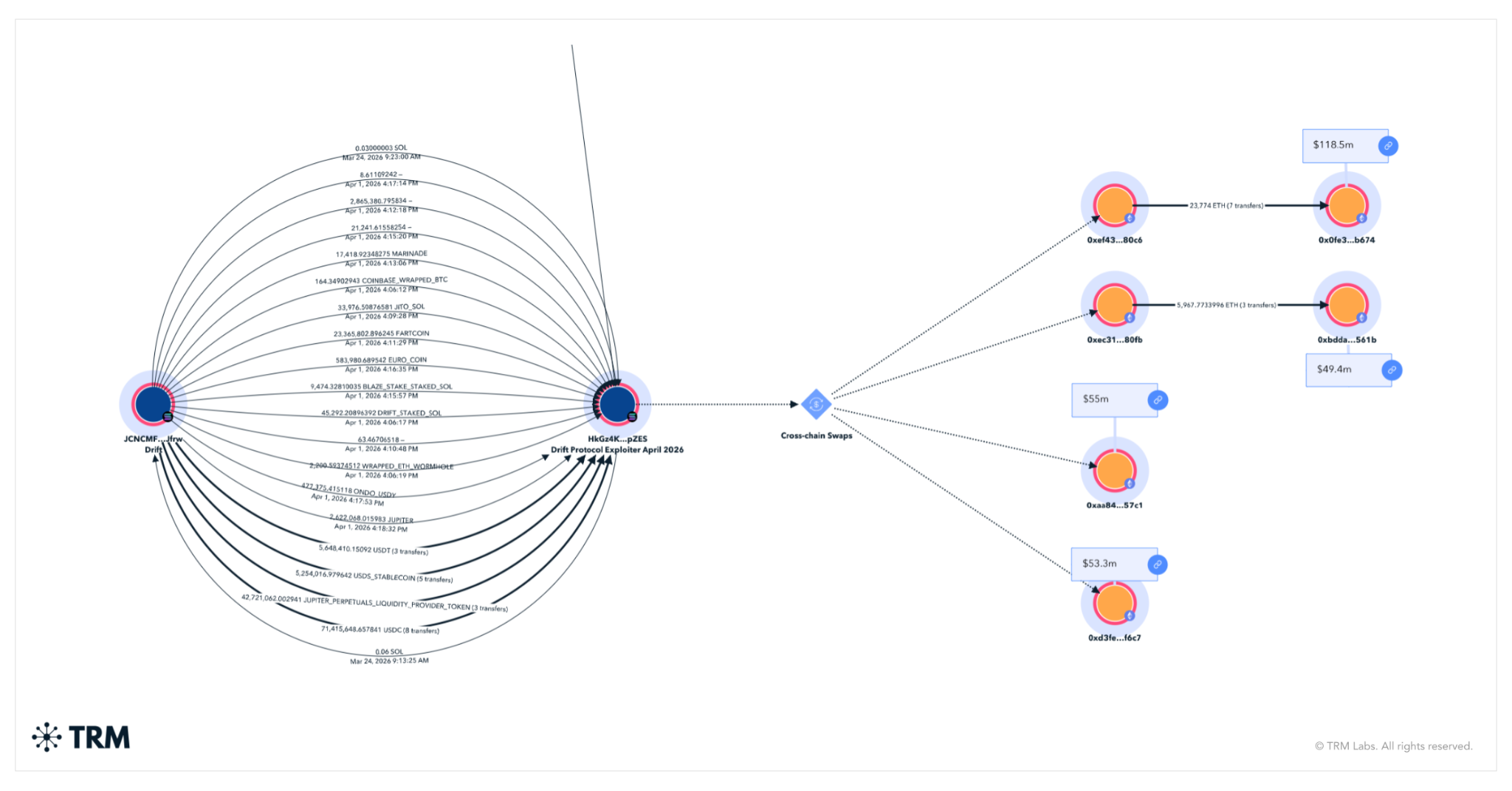
Drift suspended deposits and withdrawals. The DRIFT token fell over 40%. Many of the stolen funds had been bridged inside hours to Ethereum.
The arrogance of the hackers was staggering. Every bridging transaction moved a whole bunch of 1000’s or, extra usually, thousands and thousands in USDC, far outstripping the velocity and aggressiveness of even the Bybit laundering of 2025.
TRM Labs, which was the primary blockchain intelligence firm to cowl Solana, and has probably the most full protection of the blockchain right this moment, is actively monitoring the cross-chain funds motion and monitoring on-chain indicators associated to potential state actor involvement. Extra to come back as the image develops.
Regularly requested questions
1. What occurred to Drift Protocol?
On April 1, 2026, attackers drained roughly USD 285 million in person belongings from Drift Protocol, the most important decentralized perpetual futures trade on Solana, in roughly 12 minutes.
2. Why does TRM consider this was North Korea?
TRM’s preliminary investigation recognized a number of on-chain indicators per North Korean tradecraft, together with using Twister Money for preliminary staging, the deployment timing of the CarbonVote token at 09:30 Pyongyang time, the cross-chain bridging patterns, and the velocity and scale of post-hack laundering — all of which align intently with methods noticed in prior DPRK-attributed hacks together with the Bybit exploit of 2025.
3. How does this evaluate to different main crypto hacks?At USD 285 million, the Drift exploit is the most important DeFi hack of 2026 and the second-largest in Solana’s historical past, behind solely the USD 326 million Wormhole bridge hack in 2022. The post-hack laundering additionally exceeded the tempo of the Bybit exploit in 2025 in each velocity and transaction dimension, shifting thousands and thousands per transaction inside hours of the drain.
4. What ought to DeFi protocols do in another way in mild of this assault?
Three classes are instantly obvious. First, timelocks on governance and admin actions are a crucial safeguard — their removing, as occurred right here on March 27, eliminates the detection window that makes intervention potential. Second, oracle design requires defense-in-depth: protocols ought to require minimal liquidity thresholds, time-weighted value validation, and circuit breakers earlier than accepting any asset as collateral. Third, multisig hygiene issues — signers ought to have sturdy processes for independently verifying the total content material of any transaction earlier than signing, significantly these touching admin features.